
In summary:
- Traditional disaster recovery plans are failing against modern threats like ransomware which actively target backups.
- True business continuity isn’t achieved with a static document, but by engineering a dynamic, automated, and cryptographically isolated recovery system.
- This involves adopting advanced strategies like the 3-2-1-1-0 rule, logical air gaps, automated recovery validation, and Infrastructure as Code (IaC).
- The focus must shift from manual planning to architecting for resilience, where the recovery process is as robust and tested as the production environment itself.
As an IT manager, you live with a constant, low-level hum of anxiety. It’s the “what if” scenario: a critical system fails, data is encrypted, and the business grinds to a halt. In that moment, the Disaster Recovery Plan (DRP) is supposed to be your saving grace. But too often, it’s a multi-page document gathering dust on a shelf, its procedures untested and its assumptions outdated. The common advice—have backups, test your plan, assign roles—is not wrong, but it is dangerously incomplete in the face of today’s sophisticated threats.
There’s a fundamental distinction to make. A Business Continuity Plan (BCP) is the overall strategy to keep business functions operational during a disruption. The DRP is the technical component of the BCP, focused specifically on restoring IT infrastructure and data. The failure of the DRP inevitably leads to the failure of the BCP. And the hard truth is that many traditional DRPs are built on a foundation of hope, not engineering.
But what if the very concept of a static “plan” is the point of failure? The key to genuine resilience isn’t writing a better document, but architecting a better system. A modern DRP is not a binder; it’s an automated, cryptographically-isolated, and constantly validated machine built for one purpose: guaranteed recovery. It treats your recovery environment with the same rigor as your production environment.
This guide will walk you through the core principles of engineering such a system. We will move beyond the platitudes to explore the specific strategies that ensure your safety net is immune to attack and ready to deploy at a moment’s notice, from the gold-standard backup rule to using workflow automation as your ultimate recovery tool.
Summary: How to Create a Disaster Recovery Plan That Ensures Business Continuity?
- The 3-2-1 Backup Rule: Why Is It the Gold Standard for Data Protection?
- Backup Verification: When Was the Last Time You Tested Your Restore Process?
- AWS S3 vs Google Coldline: Which is Cheaper for Long-Term Archiving?
- Air-Gapped Backups: How to Ensure Hackers Can’t Delete Your Safety Net?
- Emergency Access: Who Has the Master Passwords If the IT Director Is Unreachable?
- SOPs: Why Documenting Your Workflow Is the First Step Before Automating It?
- Password Managers: Is It Safe to Store All Your Logins in One Cloud Vault?
- How to Use Workflow Automation to Save 10 Hours a Week for Your SME?
The 3-2-1 Backup Rule: Why Is It the Gold Standard for Data Protection?
The 3-2-1 backup rule has long been a foundational principle of data protection: maintain at least three copies of your data, store two on different media, and keep one copy offsite. While simple, its brilliance lies in creating redundancy against a wide range of failure scenarios, from hardware failure to a localized disaster. However, in the modern threat landscape, the “why” behind this rule has shifted from protecting against accidents to defending against active, malicious attacks.
The sobering reality is that attackers no longer just target your primary data; they hunt for your backups to eliminate any chance of recovery. In fact, 94% of ransomware victims had attackers attempt to compromise their backups, with those attempts succeeding in a majority of cases. This is why the classic 3-2-1 rule is evolving.
Case Study: The Evolution to the 3-2-1-1-0 Strategy
In response to the cyberthreat landscape, risk management experts now advocate for the 3-2-1-1-0 strategy. This modern framework adds two critical components. The extra ‘1’ stands for one immutable or air-gapped copy that cannot be modified or deleted by any user or process, making it invulnerable to ransomware encryption or malicious deletion. The final ‘0’ represents zero errors during backup recovery, emphasizing that a backup is worthless until its restoration has been successfully tested and verified. This approach directly addresses the dual threats of ransomware and untested restore processes, aligning with rigorous compliance standards like NIS2 and NIST.
Adopting the 3-2-1-1-0 mindset transforms your backup strategy from a passive storage task into an active defense mechanism. It forces you to ask not just “Is our data backed up?” but “Is our data recoverable, even if an attacker gains full control of our network?”
Backup Verification: When Was the Last Time You Tested Your Restore Process?
Here is the question that should keep every IT manager awake at night: when was the last time you performed a full restore from your backups, not as a drill, but to verify data integrity? A backup that hasn’t been tested is not a safety net; it’s a liability. The assumption that a completed backup job equals a successful recovery is one of the most dangerous in IT. Data corruption can occur silently, configuration drift can render backups incompatible, and dependencies can be missed.
Manual testing is sporadic and insufficient. The only way to guarantee recoverability is through automated and continuous recovery validation. This involves regularly spinning up isolated environments (sandboxes) from your backups and running automated scripts to verify that applications launch, databases are consistent, and critical files are accessible. This systematic approach turns recovery from a hopeful guess into a predictable, measurable outcome.
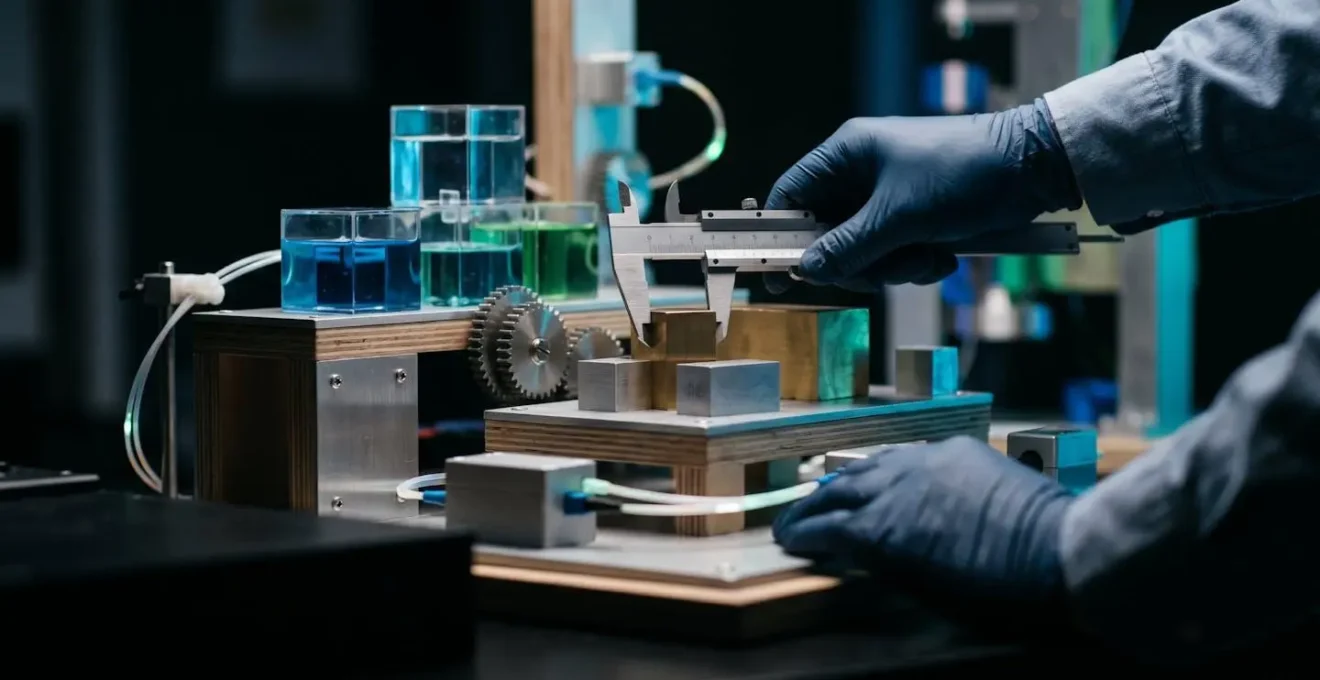
As the visual suggests, this process creates a controlled, sterile environment to prove your backups work without impacting production systems. It is the only way to truly know your Recovery Time Objective (RTO) and Recovery Point Objective (RPO) are achievable. This moves backup verification from a quarterly checklist item to a living, breathing part of your infrastructure’s immune system.
Action Plan: Implementing Automated Recovery Validation
- Define Scope & Schedule: Establish a formal restore testing plan, defining which critical resources are tested and at what frequency (e.g., weekly for tier-1 apps, monthly for tier-2).
- Automate Execution: Configure event-driven triggers (e.g., using Amazon EventBridge or similar services) to automatically initiate the sandboxed restore process based on your schedule without manual intervention.
- Implement Validation Scripts: Develop automated scripts (e.g., using AWS Lambda or PowerShell) to perform post-restore checks, verifying system connectivity, data integrity, and critical service availability.
- Monitor & Measure Performance: Actively track key recovery metrics during tests, specifically the actual time-to-recovery (your true RTO) and the rate of any data corruption or configuration errors detected.
- Audit & Report Compliance: Utilize built-in tools (like AWS Backup Audit Manager) to generate automated compliance reports, providing irrefutable proof of restoration success to stakeholders and auditors.
AWS S3 vs Google Coldline: Which is Cheaper for Long-Term Archiving?
The “one offsite copy” tenet of the 3-2-1 rule invariably leads to the cloud, specifically to cold storage tiers designed for long-term data archiving. The two titans in this space are Amazon Web Services (AWS) with its S3 Glacier family and Google Cloud with its Coldline and Archive tiers. As a risk management consultant, my advice is to look beyond the sticker price of storage per gigabyte. The true cost of archival storage is a function of three variables: storage cost, retrieval cost, and retrieval time.
A common mistake is to choose the absolute cheapest storage tier without modeling the potential cost and time of a full-scale disaster recovery. A few cents saved per month on storage can translate into thousands of dollars in unexpected retrieval fees and days of added downtime during a crisis. For example, according to a comprehensive pricing analysis, Google’s colder tiers can have lower storage costs but higher retrieval fees, while AWS offers more granular options like S3 Intelligent-Tiering to automate cost savings based on access patterns.
The following table provides a high-level comparison to guide your analysis. Your choice should not be based on which is “cheaper,” but which model best aligns with your organization’s specific RTO and budget for a worst-case scenario.
| Storage Tier | AWS S3 Pricing | Google Cloud Storage Pricing | Best Use Case |
|---|---|---|---|
| Standard (Hot) | $0.023/GB/month (first 50TB) | $0.020/GB/month | Frequently accessed data |
| Infrequent Access | S3 Standard-IA varies by region | Nearline: optimized for <1/month access | Monthly or quarterly access |
| Cold Archive | S3 Glacier pricing model | Coldline: for <1/quarter access | Quarterly access patterns |
| Deep Archive | Glacier Deep Archive: cheapest AWS option | Archive: for <1/year access, simpler pricing | Long-term retention, compliance |
| Retrieval Complexity | Multiple tiers with varying retrieval times and costs | Simpler structure, more predictable costs | Recovery scenario planning |
The decision requires a strategic trade-off. AWS provides immense flexibility and cost-optimization potential for those willing to manage its complexity. Google offers a simpler, more predictable pricing structure that may be more suitable for organizations prioritizing ease of use and budget clarity in a recovery scenario.
Air-Gapped Backups: How to Ensure Hackers Can’t Delete Your Safety Net?
The concept of an “air gap” is the ultimate defense in data protection. It refers to a copy of your data that is physically or logically isolated from your network, making it inaccessible and immune to any online attack. In a world where 59% of organizations were hit by ransomware in 2024, an air-gapped backup is no longer an optional extra; it is a mandatory component of any serious DRP. If an attacker can delete or encrypt your backups, your DRP is worthless.
Traditionally, air gaps were physical: think backup tapes transported to a secure offsite vault. While effective, this method is slow, resource-intensive, and prone to media degradation. Recovery from tape can take days or weeks, an unacceptable RTO for most modern businesses. This has led to the rise of the logical air gap, which leverages cloud architecture to provide the same level of isolation with far greater speed and efficiency.
Case Study: Modern Air Gaps with Immutable Cloud Vaults
Cloud providers like AWS now offer logically air-gapped vaults that store immutable backup copies in separate, service-owned accounts. This creates a cryptographic barrier: the backups are isolated from your primary account and protected by multi-layered, zero-trust access controls that even you, the customer, cannot bypass. This architecture makes it impossible for an attacker who has compromised your production environment—or even your administrator credentials—to access and corrupt these isolated backups. This approach provides the robust protection of a physical air gap while eliminating the slow recovery times and high overhead, enabling rapid, reliable restoration when it matters most.
Implementing a logical air gap is a critical step in building a resilient DRP. It is the most effective countermeasure against the primary tactic of modern ransomware: the systematic destruction of an organization’s recovery capabilities.
Emergency Access: Who Has the Master Passwords If the IT Director Is Unreachable?
Your DRP meticulously outlines how to restore servers and databases, but does it answer a more fundamental question: who can authorize and execute the plan if you, the IT Director, are on a plane, in a hospital, or otherwise unreachable? This “bus factor” risk is a critical, and often overlooked, single point of failure. Simply storing master passwords in a physical safe is an archaic and insecure solution. The modern approach is a formal, audited “break-glass” procedure built around zero-trust principles.
A break-glass procedure is a pre-defined and highly controlled process for gaining emergency access to the most critical credentials, such as the root account for your cloud provider or the master password for your backup system. It is not about hiding a password; it is about creating an accountable, multi-party system for its release.
As the U.S. government’s official guidance highlights, this planning is not just an IT function but a core business process. Ready.gov puts it best in their guidance:
An information technology disaster recovery plan (IT DRP) should be developed in conjunction with the business continuity plan. Priorities and recovery time objectives for information technology should be developed during the business impact analysis.
– Ready.gov, IT Disaster Recovery Plan guidance
This means your emergency access protocol must be designed with business leaders and clear accountability. A robust break-glass procedure should include the following best practices:
- Multi-Party Authorization: Require approval from multiple C-level executives (e.g., the CEO and COO) before emergency credentials can be accessed.
- Automated Alerting: Configure immediate, automated alerts to all stakeholders the moment a break-glass account is accessed, ensuring full transparency and accountability.
- Defined Succession: Document primary, secondary, and tertiary personnel for each critical recovery role, ensuring someone trained is always available.
- Mandatory Credential Rotation: Implement a non-negotiable post-event procedure to immediately revoke emergency access and rotate all associated credentials after use.
- Periodic Testing: Test the break-glass procedure during DR drills to verify that access works as expected and that all designated personnel understand their roles.
SOPs: Why Documenting Your Workflow Is the First Step Before Automating It?
“Document everything” is a common refrain in IT, but it’s dangerously misleading. The goal is not to create a 100-page novel that no one will ever read. In a crisis, dense paragraphs are useless. You need clear, concise, and executable instructions. The purpose of Standard Operating Procedures (SOPs) in a DRP is not to be read; it is to be executed under stress at 3 AM by a panicked non-expert. This realization changes everything about how you approach documentation.
This is where the “Docs-as-Code” philosophy becomes a powerful tool. Instead of using word processors, you treat your disaster recovery documentation as version-controlled code stored in a private Git repository. This approach transforms static documents into a dynamic, reliable asset.

Case Study: The ‘Docs-as-Code’ Approach to DR
By storing documentation in Git, organizations gain a clear audit trail of who changed what, when, and why. Updates can be reviewed and approved through pull requests, just like software code, ensuring accuracy and consensus. The documentation itself is formatted for crisis execution: heavy use of checklists, simple imperative language (“Run this command,” “Verify this output”), screenshots, and flowcharts. This structure ensures the SOPs are immediately actionable and leaves no room for interpretation. This process ensures your DRP documents remain current, accurate, and truly function as a guide during an emergency.
Well-documented SOPs serve another vital purpose: they are the blueprint for automation. You cannot automate a process that you cannot first clearly define. By meticulously documenting each step of your recovery workflow, you create the precise specification needed to later script and automate those actions, ultimately leading to a faster and more reliable recovery.
Password Managers: Is It Safe to Store All Your Logins in One Cloud Vault?
The question of whether to use a password manager for disaster recovery credentials creates a paradox. Is it wise to place all your critical keys in one basket? The alternative, however, is often far worse: scattered passwords on spreadsheets, in insecure documents, or in the heads of a few key employees. From a risk management perspective, the answer is clear: a centrally managed, enterprise-grade password manager is not only safe but essential, provided it is implemented with a specific DR strategy.
The risk of not having immediate access to credentials during an outage is catastrophic. With the average cost of downtime being $14,056 per minute, any delay in recovery is immensely expensive. A properly configured password manager mitigates this risk by ensuring the right people have access to the right credentials at the right time.
The key is to not treat your DR credentials like everyday passwords. A robust strategy involves several layers of protection:
- Select for Offline Access: Choose an enterprise-grade manager that offers a cached or offline mode, ensuring you can access credentials even if cloud services or your own internet connection is down.
- Create “Break-Glass” Vaults: Within the password manager, create separate, highly restricted vaults specifically for DR credentials. Access should be governed by your break-glass procedures with robust auditing.
- Segregate Credentials: Never mix day-to-day operational passwords with disaster recovery credentials. This prevents accidental exposure during routine use and limits the blast radius if a standard user account is compromised.
- Store More Than Passwords: Use the secure notes feature to store critical non-password information needed for recovery, such as recovery keys for encrypted volumes, cloud provider support PINs, and key vendor contact details.
- Maintain a Physical Failsafe: For the absolute bare-minimum credentials needed to initiate recovery (e.g., the password manager master password itself), maintain a physical emergency kit, such as an encrypted USB drive stored in a secure vault.
A password manager isn’t just a vault; it’s an access control system. By leveraging its features correctly, you can build a secure, audited, and resilient system for managing the keys to your kingdom.
Key takeaways
- Shift from static DRP documents to dynamic, engineered recovery systems. A plan is not what you write; it’s what you build and automate.
- Prioritize cryptographic isolation and immutability. Your safety net must be invulnerable to the very threats you’re protecting against, especially ransomware.
- Embrace continuous, automated validation. An untested backup is a liability. Recovery must be a predictable, repeatable, and measured process.
How to Use Workflow Automation to Save 10 Hours a Week for Your SME?
While the title suggests time savings for routine tasks, the most profound impact of workflow automation is realized during a disaster. In a crisis, automation is not about efficiency; it is about eliminating human error under extreme pressure. The ultimate goal of a modern DRP is to transform the recovery process from a frantic, manual scramble into a calm, predictable, push-button operation. This is achieved through Infrastructure as Code (IaC) and automated communication workflows.
Instead of trying to “fix” compromised systems, a modern DRP leverages automation to deploy brand new, clean environments from scratch in minutes. This is the core principle of treating your infrastructure as disposable and your data as sacred.
Case Study: Infrastructure as Code for Rapid Recovery
Organizations leverage IaC tools like Terraform or AWS CloudFormation to define their entire server, network, and application infrastructure in version-controlled code. This code is the ultimate “executable documentation.” In a disaster, instead of following a manual checklist, an engineer executes a single script. This script automatically provisions a new, identical, and clean environment in the cloud, connects it to the restored data, and brings the system online. This automated, repeatable workflow eliminates human error, ensures consistency, and reduces recovery time from days to minutes.
This automation extends to stakeholder communication. Tools like Statuspage.io can be integrated with monitoring systems via PagerDuty or Zapier. When a system fails, updates are automatically posted to customers and internal teams. When recovery milestones are reached, the status is updated again. This frees your technical teams from the communication overhead, allowing them to focus entirely on restoration.
Stop treating your disaster recovery plan as a compliance checkbox that gets audited once a year. Start architecting a resilient, automated system designed for the realities of modern threats. The first step is to audit your current backup strategy against the 3-2-1-1-0 framework and identify your most critical gap: is it immutability, offsite storage, or verified recovery? Address that first.